Objective: Sniff and intercept HTTP/HTTPS traffic sent from an Android device (phone or tablet) that does not have root access.
If you have a rooted Android device, you can sniff all the HTTP and HTTPS traffic using Shark for Root, a tcpdump based sniffing app. But, even with such an app, you will not be able to decode HTTPS traffic.
If you do not have a rooted Android device, and if you want to sniff HTTP/HTTPS traffic, you will need to use a MITM (man-in-the-middle) proxy that is capable of sniffing SSL traffic.
How MITM Proxy Method Works
In short, the following diagram explains the traffic flow with a MITM proxy.
The phone (P) is configured to use the MITM proxy (M) via a Wi-Fi network (AP). All HTTP/HTTPS traffic from the phone will pass through the MITM proxy. The MITM proxy will then forward the HTTP/HTTPS request from the phone to the required destination server (S). As long as the client certificates have been installed on the Android phone, the MITM proxy will be able to decrypt the HTTPS traffic sent from the Android device.
As for the response from the destination server, it will be sent to the MITM proxy. The MITM proxy will then forward this response back to the phone over the Wi-Fi network.
Network Setup
For the MITM proxy, we will be using mitmproxy. It can be installed on both Linux and Windows. For this article, I will use a Linux machine. On Debian based (Ubuntu, Kali, etc) Linux, you can install the software using the following syntax.
|
1 |
$ sudo apt-get install mitmproxy |
Once installed, start the proxy. It will listen on all interfaces on port 8080. Note that this MITM proxy (M) and the Android device (P) must reside on the same (Wi-Fi) network.
|
1 |
$ mitmproxy |
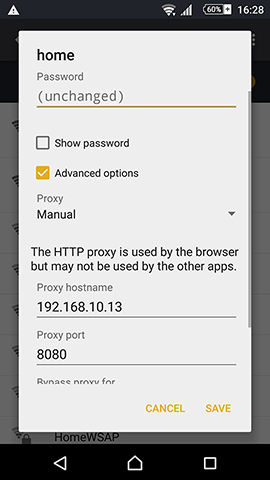
Next, enable Wi-Fi on the Android device. Then, modify the Wi-Fi settings and add the MITM proxy address. For my case, the PC (M) running mitmproxy has an IP of 192.168.10.13 and the port is 8080. My phone has an IP of 192.168.10.14. Both my Android phone and the Linux PC are on the 192.168.10.0/24 network.
Next, on your Android device, open up your browser and visit the site mitm.it. Click on the Android icon and follow the setup instructions to install the client certificate.
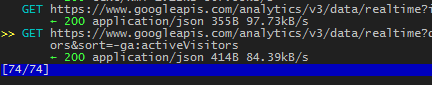
Now, the MITM proxy should be ready to intercept traffic from the Android device. You will now see all the HTTP/HTTPS requests from the Android device on the terminal window where the mitmproxy process was started.
You will be able to view every individual HTTP/HTTPS request and response from the mitmproxy console. For more information on how to navigate through the mitmproxy console, refer to the documentation here.
Final Words
If you intend to sniff large amount of data, use mitmdump instead of mitmproxy.
This method will only work when the Android device is using Wi-Fi for internet access. It will not work if the Android device is using mobile data.
This method of intercepting traffic does not work with certain apps, most notably WhatsApp. From what I know, WhatsApp checks the certificates on the server before sending any traffic.