Category Archives: security
Disable Nginx Version Number in HTTP Headers
By default, Nginx sends the version number in the HTTP response. Hackers can use this information to try and exploit any known vulnerabilities in Nginx, especially if you are running a version with known vulnerabilities. Security wise, it’s a good practice to not reveal versions numbers of the HTTP server.
Extract WhatsApp Password on Android
WhatsApp uses a customised version of XMPP (Extensible Messaging and Presence Protocol) as the communication protocol. Upon installation, it creates a user account using one’s phone number (with country code prefix) as the username (Jabber ID: [phone number]@s.whatsapp.net). A password is generated using an unknown algorithm on the server end and sent to the client. Previously the password was derived from the phone’s IMEI or the WiFi MAC address.
Session Hijacking
Session hijacking or cookie hijacking is a way to exploit a valid computer session and gain unauthorised access to information or services in a computer system. It mostly refers to the theft of HTTP cookies that are used to authenticate a user on a web server. In this article, I am going to show you how to perform session hijacking on a website running on WordPress.
Offline Heartbleed Vulnerability Scanner Tools
Numerous online Heartbleed vulnerability scanners have popped up recently. These sites claim that they are able to identify websites that are vulnerable to the OpenSSL Heartbleed bug. So what happens if one of the Heartbleed scanning websites concludes that your site is vulnerable? It means that the owners of the scanner websites know that sensitive data can be retrieved from your site by exploiting the Heartbleed bug.
How to Decrypt WhatsApp crypt5 Database Messages
A couple of weeks back, WhatsApp introduced a new way of encrypting the backup messages saved on the SD card. The article that I wrote last month on decrypting the WhatsApp messages will no longer work on the new crypt5 files.
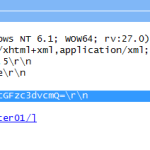
Decode HTTP Basic Access Authentication
HTTP Basic Access Authentication is a simple challenge and response mechanism to enforce access controls to web resources. It does not require overheads like cookies, session identifiers, login pages, etc. Since this method is on the weak end of the security strength spectrum, it is seldom implemented except on home Wi-Fi routers.