Tag Archives: security
Disable Nginx Version Number in HTTP Headers
By default, Nginx sends the version number in the HTTP response. Hackers can use this information to try and exploit any known vulnerabilities in Nginx, especially if you are running a version with known vulnerabilities. Security wise, it’s a good practice to not reveal versions numbers of the HTTP server.
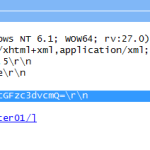
Decode HTTP Basic Access Authentication
HTTP Basic Access Authentication is a simple challenge and response mechanism to enforce access controls to web resources. It does not require overheads like cookies, session identifiers, login pages, etc. Since this method is on the weak end of the security strength spectrum, it is seldom implemented except on home Wi-Fi routers.
Bypass Android Pattern Security Lock
If you have an Android phone that is rooted and the USB Debugging option has been turned on, your phone can be unlocked in a matter of seconds with the ADB (Android Debug Bridge) utility.
How to Completely Wipe Hard Disk Contents
If you are planning to discard your old hard disk, make sure that they do not contain any valuable information when they head out of your door. The last thing on your mind is the potential of having your identity stolen from sensitive information stored in that hard disk.
Symbolic Link Exploit with Temporary Files Created in Shell Scripts
Many coders do not think that creating temporary files in a secure way is important, especially in shell scripts. It’s just a temporary file, they might say. But a simple symbolic link exploit could make the whole system unusable.
Enable Windows NTLM Authentication in Firefox
Windows NTLM (NT Lan Manager) is a Microsoft authentication protocol used with the SMB (Server Message Block) protocol.
A lot of the protocol was reverse engineered by the Samba team – the people behind the Samba server that allow UNIX machines to share files and printers with a Windows client.
Windows Vista User Account Control (UAC) Alternative
User Access Control (UAC) was introduced as a security infrastructure in Microsoft Windows Vista. It aims to improve the security of Microsoft Windows by limiting privileges of application software. Any request for an increase in privilege level has to be authorised by an administrator. In this way, only trusted applications receive higher privileges.