In modern UNIX and Linux systems, user passwords are encrypted and stored in the /etc/shadow file. On BSD systems, the passwords are kept in the /etc/master.passwd file. The encrypted password field in the file contains more than just the encrypted password, it contains additional information.
The shadow password file can only be read by a superuser or by root, therefore you will need to login as root before you can start exploring the file.
UNIX shadow password hashing
Before looking at the contents of the file, we need to have some basic understanding on how the passwords are hashed in UNIX.
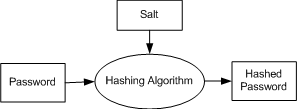
To get the encrypted password, a password hashing algorithm is required. This algorithm is not fixed and varies between different UNIX systems. The password hashing algorithm used for one user could be different from the one used for another user even on the same UNIX system. Another required input is the salt used by the hashing algorithm to encrypt the password. Therefore the stored password field must also contain the hashing algorithm and the salt used for hashing the original password.
Contents of /etc/shadow file
The format of the shadow password file is the same as that of the /etc/passwd file: one line per user, ordered fields per line separated by : (colons). On my Ubuntu server VM running on VirtualBox, my shadow entry is stored as follows:
|
1 2 |
# cat /etc/shadow | grep ibrahim ibrahim:$1$hanhd/cF$3lzrzB14HceT7uc3oTmog1:14323:0:99999:7::: |
The encrypted password is stored in the second field – $1$hanhd/cF$3lzrBC14HceT7uc3oTmog1. As I mentioned earlier, this field contains additional information. If you notice, there are three $ characters in the field.
If the field begins with $digit$, then the Modular Crypt Format is used. If the entry does not start with a $, but instead of a _ (underscore), then the DES Extended Format is used. If the field neither starts with $ or _, then the Traditional Format is used.
Modular Crypt Format
As far as I know, this is the most popular format, and therefore we will only cover this format. Password fields starting with $digit$ belong to the Modular Crypt Format.
- $1$ – MD5
- $2$ or $2a$ – Blowfish
- $5$ or $6$ – SHA
The second sub-field between the second and third $ character is the salt used in the encryption. In our case the salt is hanhd/cF. The sub-field after the third $ is the actual hashed password field.
User Authentication
Once the password is hashed, it is almost impossible to retrieve the original password except by brute force attacks. The user is authenticated by hashing the entered password and comparing the string with the stored hashed password. If the strings match, the user is assumed to have entered the correct password.

